Token authentication blocks requests to your Pull Zone unless a valid signed token is included. Use it to protect premium content, create expiring download links, or restrict access by country or IP.Documentation Index
Fetch the complete documentation index at: https://docs.bunny.net/llms.txt
Use this file to discover all available pages before exploring further.
Choose a method
Both methods can be used on the same Pull Zone. Start with Basic for simple expiring URLs. Use Advanced if you need geo-restrictions, directory-level access for video streaming, or speed limits.
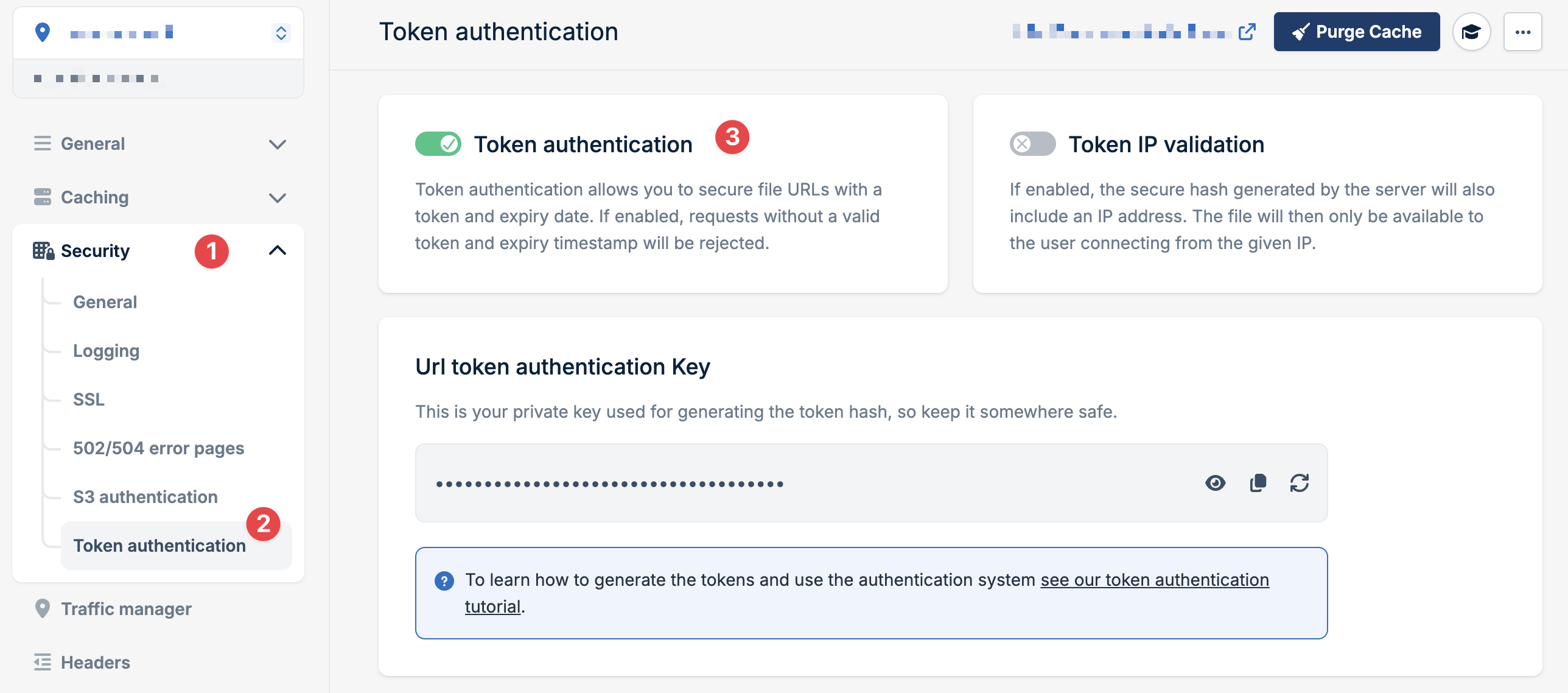
Enable token authentication
How it works
Your application signs each URL by creating a hash from your security key, the URL path, and an expiration time:IPv6 is automatically disabled when token authentication is enabled.